
This course covers security testing methods, criteria for selecting security testing techniques, individual test steps, and their role in the development lifecycle. Dates available upon request.
more info
This course covers security testing methods, criteria for selecting security testing techniques, individual test steps, and their role in the development lifecycle. Dates available upon request.
more info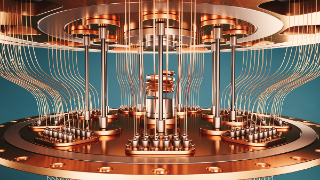
This course provides an overview of the fundamentals of quantum mechanics, quantum gates and circuits, as well as quantum programming. It also covers key algorithms and application areas. The course starts on March 17, 2025.
more info
A two day workshop for small and medium-sized enterprises that want to take a strategic and practical approach to digitalization.
more info
This one-day management-level course addresses the critical gap between understanding the EU AI Act and being able to prove compliance through documentation. It explains how AI use cases are classified by risk, what documentation must exist for each class, and how documentation can be structured in a risk-driven, lifecycle-oriented, and reusable way.
more info
The training provides a clear understanding of how the railway system works and why railway projects come with unique requirements. Participants gain a compact overview of safety, RAMS and the most relevant standards, along with their impact on project work. Ideal for anyone who wants to realistically assess and effectively prepare for railway projects.
more info
This course provides foundational knowledge and practical skills for integrating large language models (LLMs) into applications and workflows.
more info
This course provides a comprehensive introduction to securing Continuous Integration /Continuous Delivery (CI/CD) systems and enables participants to implement secure systems right from the start.
more info
The course provides an introduction to structured security testing processes in the context of different application lifecycle models. It explains the tasks and methods of the individual testing phases in a hands-on way, including typical vulnerabilities and organizational aspects.
more info
BCM enables organizations to effectively respond to challenges such as cyberattacks, natural disasters, technical failures, and human error. The next sessions will take place from June 24–26, 2025, and November 26–28, 2025.
more info
This course provides the opportunity to develop an independent IT security concept based on the threats outlined in the IT-Grundschutz Compendium, enabling targeted risk management. The next session will be on 12th of November 2025 (registration until 29th of October 2025)
more info